D2iQ Kommander
Enterprise Kubernetes Cluster Governance and Control








Why Use D2iQ Kommander?
Manage Applications and Infrastructure Declaratively
Simplify Application and Cluster Lifecycle Management
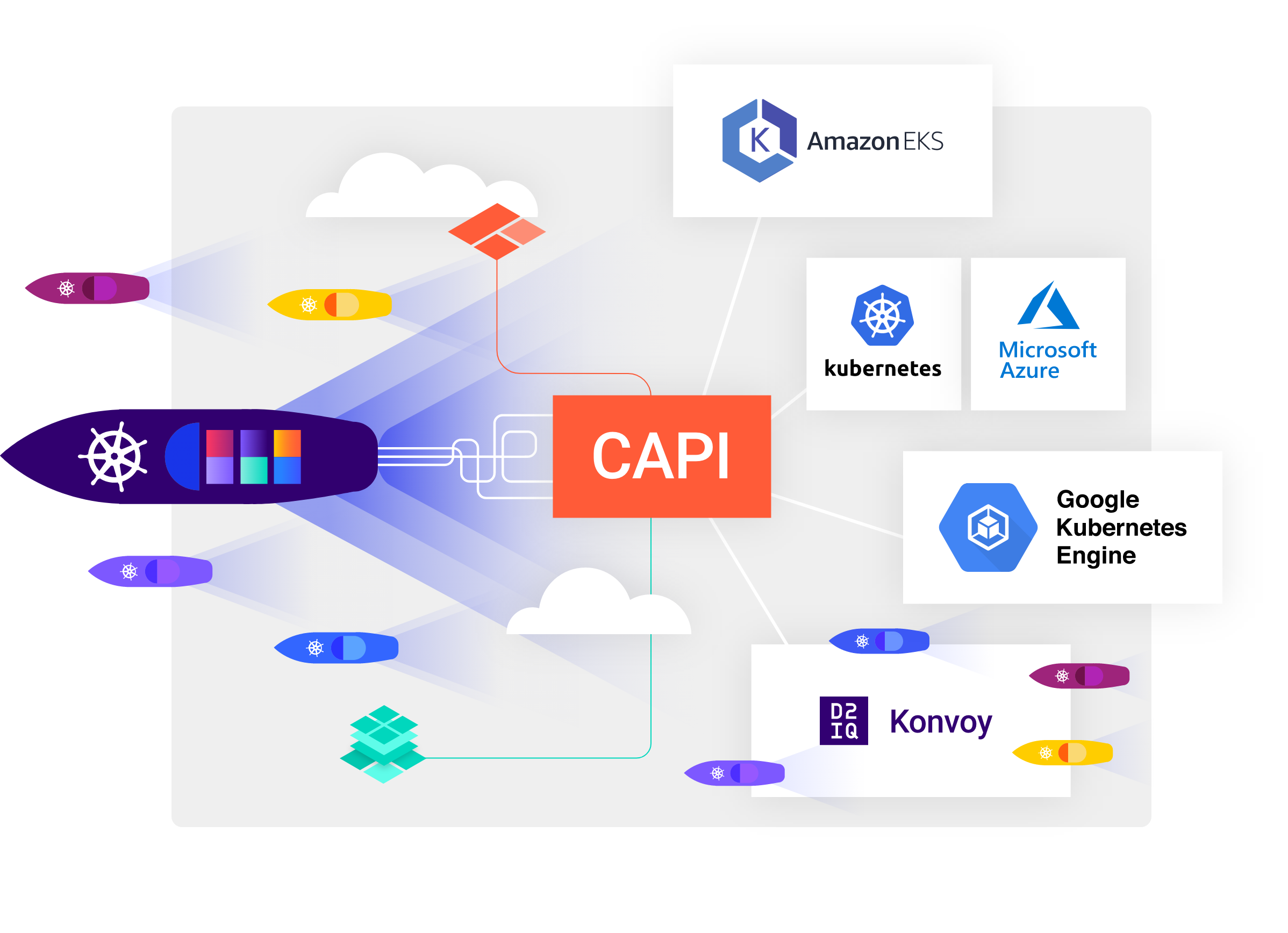
Provide Real-Time Cost Management
Lower TCO with Out-of-the-Box Kubecost
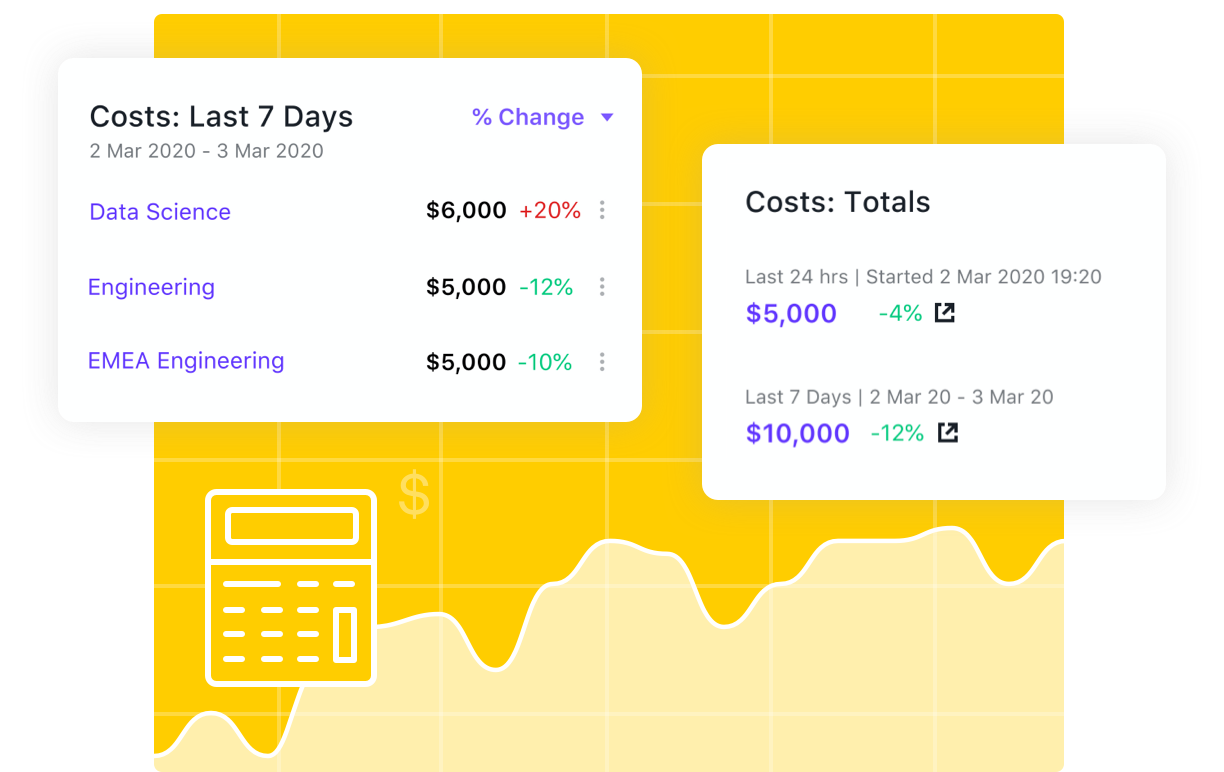
Enable Centralized Observability for Easier Troubleshooting
Enhance Logging and Monitoring Across Clusters
Deliver Federated Management Across a Wide Variety of Roles
Provide Enterprise Access Controls for Multi-Tenancy
Ensure Unified Management and Governance
Manage Risk and Security Vulnerabilities
Features and Benefits
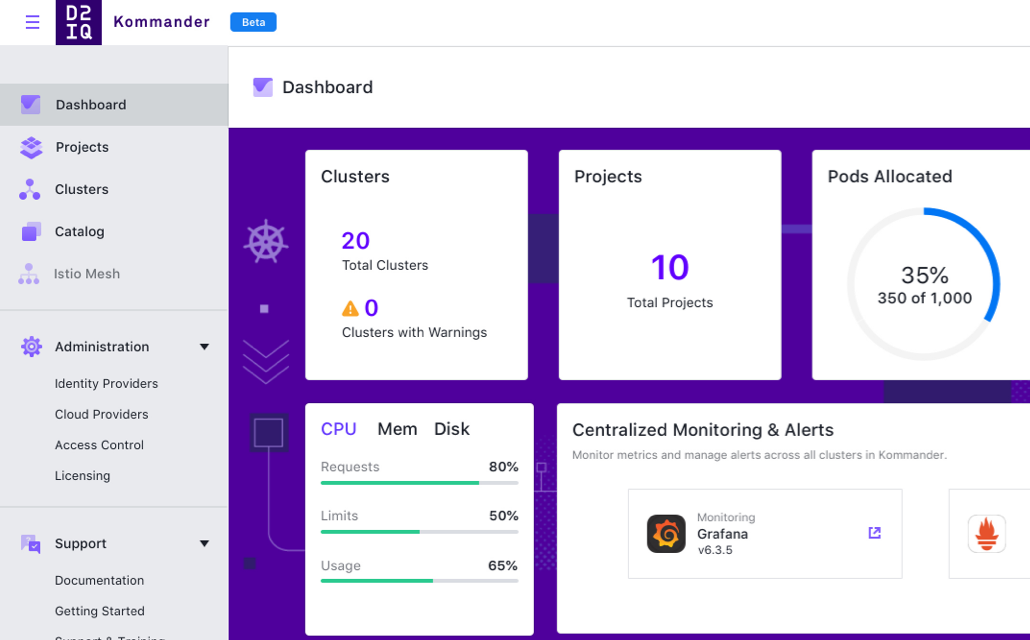
Operational Dashboard
Provide instant visibility and operational efficiency into the Kubernetes landscape from a single, central point of control.
Integrated GitOps Workflows
Enable declarative end-to-end application lifecycle management with built-in FluxCD, as well as canary and A/B deployments and roll-back.
Out-of-the-Box Kubecost
Provide real-time cost management and attribution of costs to the right groups, applications, or projects for better forecasting and lower TCO.
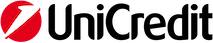
EKS and AKS Lifecycle Management
Provision, spin up, and deprovision EKS and AKS clusters in a fully automated way.
Multi-Cluster Platform Application Management
Centrally manage and deploy all Day 2 platform applications, such as logging, monitoring, networking, and more, to any CNCF-conformant Kubernetes distribution from any environment, with governance.
Service Mesh Integration
Add advanced networking capabilities, such as multi-cluster and cross-cluster service discovery, load balancing, and security, across a variety of hybrid cloud, multi-cloud, and multi-cluster environments.
Governance and Policy Administration
Assert centralized delegated Role-Based Access Control (RBAC) and cluster policy to govern clusters and services and create lines-of-separation across various project initiatives.
Centralized Authentication
Leverage existing authentication and directory services for secure access and single sign-on to broad cluster-based resources.
Service Version Control
Ensures conformance to sanctioned service versions of both Kubernetes and its supporting platform services to help reduce security exposure and provide simplified supportability of services.
Data Pipeline Provisioning
Provision Spark, Cassandra, and Kafka automatically from the Kommander catalog of platform applications.
Node Pool Management
Reduce complexity with single command cluster creation and removal.
D2iQ Resources for Enterprise Kubernetes Success
Because DKP comes with a dashboard that enables all of these services on any cloud platform, it really helps our customers focus on the applications they want to develop.